Avast firewall rules. Avast Firewall Won't Start 2019-03-05
How to Configure Avast Internet Security Firewall

These networks, referred to as ' Friends', are exempt from default Firewall restrictions that affect unknown networks. Click Next and make sure Allow the Connection is selected, then click Next again. Reducing this number saves disk space but means your Firewall Logs contains less history. But for that, you need to uninstall the program completely. It is commonly known as virus scanning or signature-based detection. Friends exemptions only apply while you are connected to Private networks.
AVAST Firewall Settings vs Windows Firewall settings
To return to the main Firewall screen, click Close in the bottom-right corner of the Firewall logs. About the Author Melly Parker has been writing since 2007, focusing on health, business, technology and home improvement. But if you are not able to do so, connect with tech experts immediately. Tech specialists are always there for you. To secure your databases, legal documents and other files from any external interruptions, configure firewall security just by taking help from the technical experts. Other predefined packet rules are created when you change the setting of a rule on the screen.
Firewall

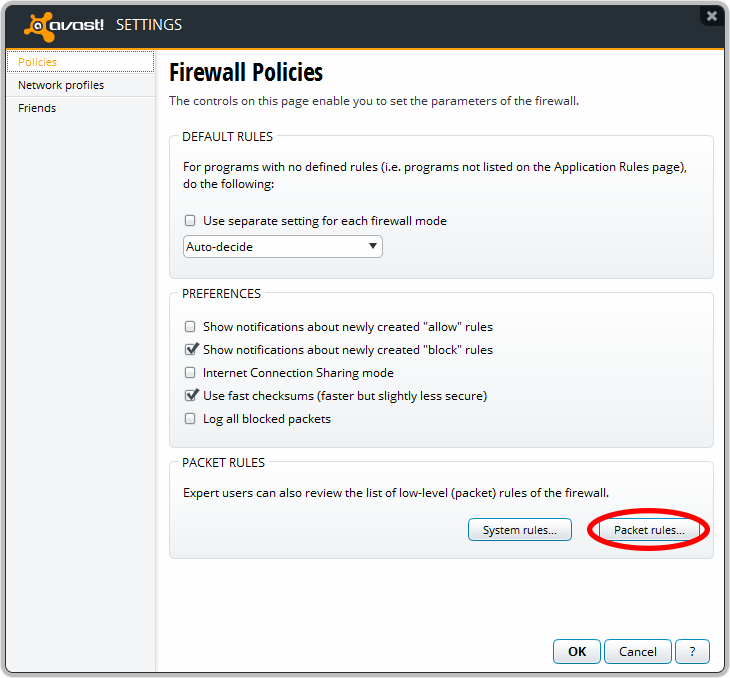
To access Network connections: To return to the main Firewall screen, click Close in the bottom-right corner of the Network Connections screen. Although you can manage your network Firewall profiles on this screen, each time you connect to a new network, Avast prompts you to select the appropriate profile. If you are looking for a platform with less clunk, and easy-to-understand user interface, you might be better off looking for another antivirus software. Once done, go back and see if Avast Firewall turns on. Note: We recommend you only make alterations to packet rules if you have advanced knowledge of firewall concepts. Now you are able to resolve your problems.
How to Configure Avast Firewall Security?
After installing and the 1st reboot, ZoneAlarm has the following firewall entries for Avast Free: I have set ZoneAlarm to always allow the following 4 items: 1. Open Malwarebytes and perform a deep scan, to see if the problem lies therein. The firewall checks the files and connections coming from outside your computer to see whether they pose a threat and, if they do, it blocks them. You also have the option to chat with officials and get the most suitable solutions instantly. I was able to remove them but I just wanted everyone to be aware in case you care. If you have another firewall running, it may be preventing Avast from opening. These rules determine how Firewall behaves toward each application or process when it connects to the internet or to another network.
Avast Firewall Won't Turn On? Here's How to Fix It [Latest]

Adjust access restrictions You can set connection allowances for each application or process to determine how strictly Firewall monitors incoming or outgoing communication. QuickBooks 2015: S019, 56725, 55363-55367. Their support specialists will answer your questions and help you solve any problems you might be experiencing. One protocol may be selected, or All if the rule applies to all protocols. I figured that but I wasn't sure if perhaps you were using Avast's firewall.
Avast Antivirus: Firewall Packet rules

In most cases, Firewall formulates optimal rules without your input. This option is only available for some network protocols. Asking users to download a browser toolbar is a rather unusual solution. QuickBooks 2011: 8019, 56721, 55343-55347. In fact, you can avail round the clock to provide you relevant and the most suitable solutions for these kinds of Avast problems. Note: Firewall is available in Avast Premier and Avast Internet Security only.
Settings
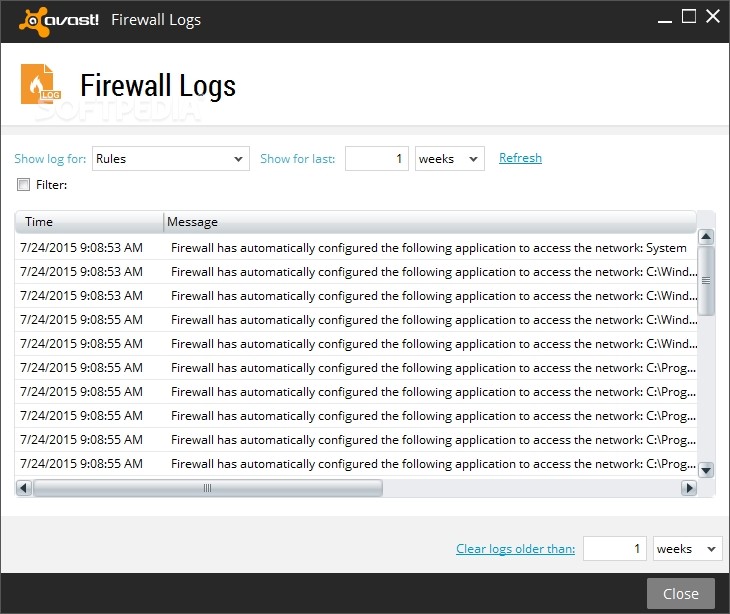
Click Refresh to update the log using your defined criteria. Restart your computer system and then start Avast. If one of your friends install it, you get a free Avast Pro Antivirus for six months. The default profile setting when no profile is selected is Public. Known malware are those that have been discovered before. I have win 7; not 10, so I don't think I can fairly comment on the Win 10 firewall although I'm guessing it's the same thing really.
Avast AV adds 2 rules to firewall

I only do manual updates. Like most antivirus software, depends on digital channels for support. So you need to scan your computer Avast. Firewall uses packet rules to control network traffic using specified connection parameters, while only control traffic according to individual rules for programs or services. Setting up on your computer does not require any special requirements. Most predefined packet rules cannot be edited.