Avast filezilla blocking. Avast detected virus on official FileZilla installer. : antivirus 2019-03-19
FileZilla Has an Evil Twin That Steals FTP Logins
CyberCapture locks down and submits potentially malicious files, including all the associated metadata, to the clean-room environment of our Avast Threat Labs, while informing the user and keeping him engaged throughout the process. If a particular file name has been targeted by nasty people, I'll just submit the one on machine for analysis by one of the many on-line anti-malware sites that attend to such things. But this isn't unique to open source code, the same attacks can be performed on binaries too if you control the original distribution point. The remote end is not entitled to make assumptions about what range ephemeral ports may be allocated from by the opposite end. And a malicious payloads could be basically anywhere in the executable, so every part is security-relevant. So I just unpackaged my computer after moving back to the states been in storage since Oct 1st. The approach is still good, but since it already involves distributing the source code, it would make No need to be condescending.
Avast is blocking my router's ip

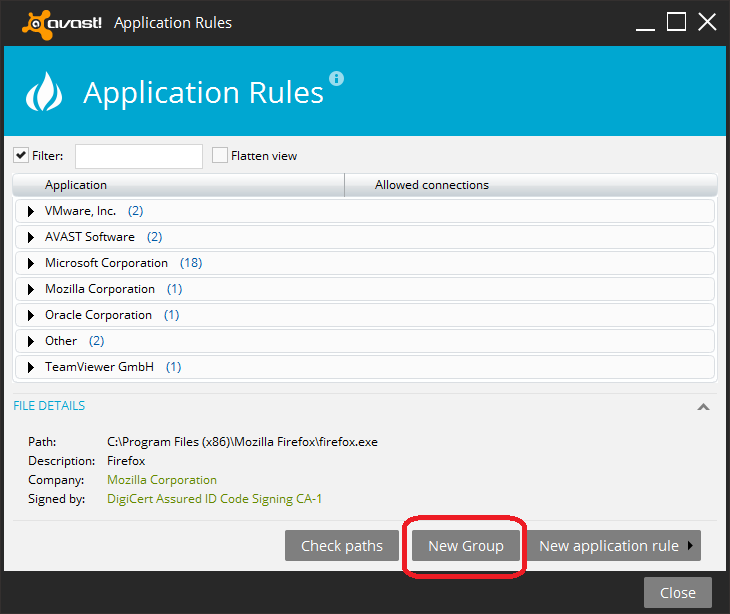
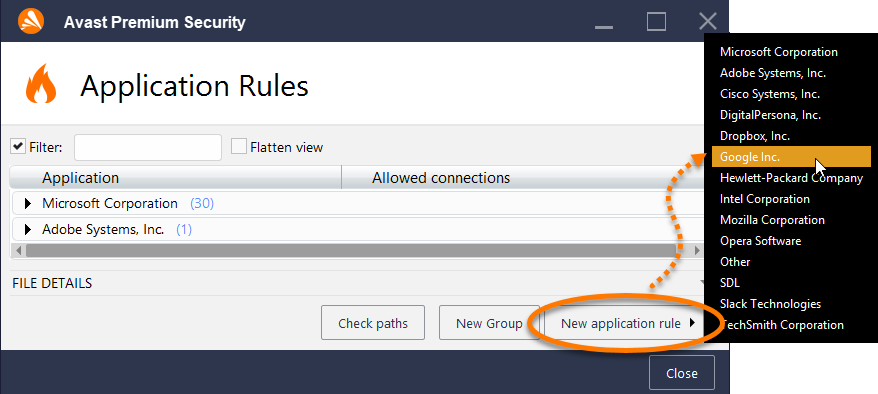
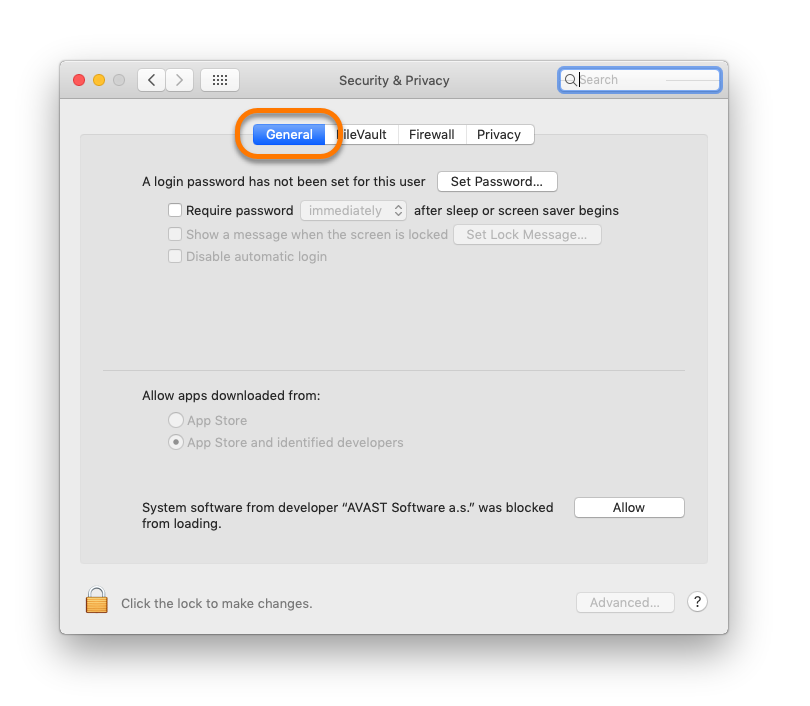
The author s then sign their software using that certificate. When finished, it shall produce a log for you. Thinking that you will be secure by putting bad domain names into your host file will tead to tears of failure because: a it's attempting to enumerate badness. So I don't quite understand why it keeps blocking the process. Next, click Yes to confirm. I checked the forum before posting and though I use both Avast as an Antivirus and ZoneAlarm as a firewall,none of them are blocking the programm to connect to whatever and whenever it wants to. Depending on optimization flags, the compiler may even restructure it differently, with no practical way to isolate security-relevant portions that should remain unchanged.
Warning: Tainted FileZilla doppelgangers want to steal your data
What the hell makes you think that the filename is an indicator of its contents? I would anticipate even a modern vintage installing on such a platform in less than a week. The official version's Nullsoft installer is v2. Run Avast Clear and say yes to rebooting into safe mode to perform cleaning 5. The only differences that can be seen at first glance are smaller filesize of filezilla. I had found this site before commming here. There's always new badness, you can't enumerate it all. Next, go to Real-Time Shields, Web Shield, and then click Stop to disable Web Shield.
FileZilla Has an Evil Twin That Steals FTP Logins
By peeling off layer by layer with deep dynamic introspection, the generic unpacker component is able to unveil known malware samples that could be hidden in heavily obfuscated and encrypted ones. . I forget whether it is 60G or 120G. Does temporarily disabling the firewall resolve the issue? To add the website to the Exclusions list, double-click the Avast icon on the system tray then go to Real-Time Shields, Web Shield, Expert Settings, and then select Exclusions. Various fingerprints, spread over security-sensitive parts of the software. On limited hardware for which there's no builds and which benef Without a doubt this will be used as propaganda against the entire Open Source community. There is a system under cygwin to download software and maybe that is what most people use.
Avast is blocking my router's ip

Absolutely, side channels are everywhere if all you care about is small packets of data. No personally identifiable information is ever collected. Either you compile from source which you can first check against a known cryptographic checksum, or you run binaries that have been cryptographically signed by the developer. I got this message whenever I run Filezilla and so must re-shape the windows and my previous read files every time. When it comes back up, again no connection. If you receive the banner from the server if one is set then great.
CuteFTP blocked by Avast Internet Security 9x

The author s of individual software programs acquire a code-signing certificate from a certificate authority that Microsoft trusts for that purpose. This is really strange, I never heard before that many wifi stations can disturb each other, but the wifi is working sometimes really slow, and with ethernet connected there are no problem. We have a hardworking team of professionals in different areas that can provide you with guaranteed solutions to a blend of your problems. If a driver is identified in the Stop message, disable the driver or check with the manufacturer for driver updates. Our cutting-edge technology transforms our users into a worldwide network of cooperating sensors.
Warning: Tainted FileZilla doppelgangers want to steal your data
:max_bytes(150000):strip_icc()/why_use_ninite-5a831a188023b90037c034b5.png)
The app store could easily be expanded to offer desktop versions of software, in addition to tablet and phone versions. During install, users can easily see the offer, and can choose to override unchecky's deselect, and install the offer anyway. I remember being pissed by that once. The malicious version is fully functional, uses the same graphical interface and component file names as the original, and masks itself further by avoiding any suspicious entries in the system registry, overt attempts to communicate with outside servers or other changes, according to the Jan. Connect everything and it doesn't recognize the Ethernet connection to the Internet. As a result, we produce quality content on a variety of subjects.
CuteFTP blocked by Avast Internet Security 9x

He advised us, that there are problems with wifi when many users are using it in the same house. What is a false positive? The most obvious differences are that the poisoned version of filezilla. Browse other questions tagged or. Please stop using these things are identifiers for malware. Does temporarily disabling the firewall resolve the issue? After that, I did a full scan with Avast Free, and it detected something like 1700 infected files.