Av comparatives crowdstrike. Bitdefender GravityZone Elite Tops AV 2019-02-08
What makes for truly independent security product testing?
The sooner the threat is detected in the exploit chain, the easier it is to remove the malicious files from the system, the less information can be gathered from the system by the attackers, and the lower the risk of an attack targeting the particular security solution on an endpoint. In emails and on social media, they outlined ways to ensure such testing is as ironclad and useful as possible. Since 2001, Bitdefender has consistently produced award-winning business and consumer security technology, and is a provider of choice in both hybrid infrastructure security and endpoint protection. We had reached out to many leading vendors in this space, requesting their participation in the test. If one network product alerts that malicious binary has been downloaded to the endpoint, administrators have to cross-check the alerts with the endpoint protection alerts, or do a full forensics investigation to be sure that no malware was running on the endpoint. Manually verifying the successful remediation of the malware in an enterprise environment is a very resource-intensive process and costs a lot of money.
CrowdStrike
Salted Hash reached out to Symantec for comment. Seriously, the security space is small and we're all friends. We believe that such zero-tolerance scoring helps enterprises to choose the best products, using simple metrics. Naked Security reached out to security practitioners for their view on the subject. A place to ask security related questions.
Bitdefender GravityZone Elite Tops AV
This process can be time and resource consuming, which is why it is better to block the exploit before the shellcode starts. I'm having a hard time finding any information at all with regards to Crowdstrike's ability to stop threats. Before the exploit site was tested, it was verified that the endpoint protection had been updated to the latest version with the latest signatures and that every cloud connection was working. In our opinion, test reports without this data and evidence should be rejected. I would love to know if anybody is.
Cylance accuses AV

A total of 21 test cases have been tested. GravityZone Elite Security is a layered next-gen security solution that combines preventive controls and multi-stage detection technologies including tunable machine learning, behavioral analysis, anti-exploit and integrated sandbox to automatically stop advanced file-based and fileless threats with speed and accuracy. In this test, 1000 non-malicious applications have been used to measure the ability of the products to distinguish clean from malicious files. In many cases, he said instances where a test is advertised as independent turn out to be false. At the time of the tests, two exploit kits dominated the Internet.
Cylance accuses AV
I agree that the reviewer should not have used dubious methods to obtain the product, but would you not agree that the reviewer shouldn't need to resort to those methods to begin with in order to review your product? The test results name Cylance as the clear winner, but while showing results for the others, the test doesn't name them directly. The test scenarios included fileless malware, exploits, command-line attacks, PowerShell-based attacks, malicious emails, and brand-new malware and ransomware samples. So the biggest struggle I've had with Crowdstrike is finding any independent reviews of the product. Good to hear from you. We look forward to their future participation in independent tests.
Opinions on Crowdstrike and Cylance? : AskNetsec
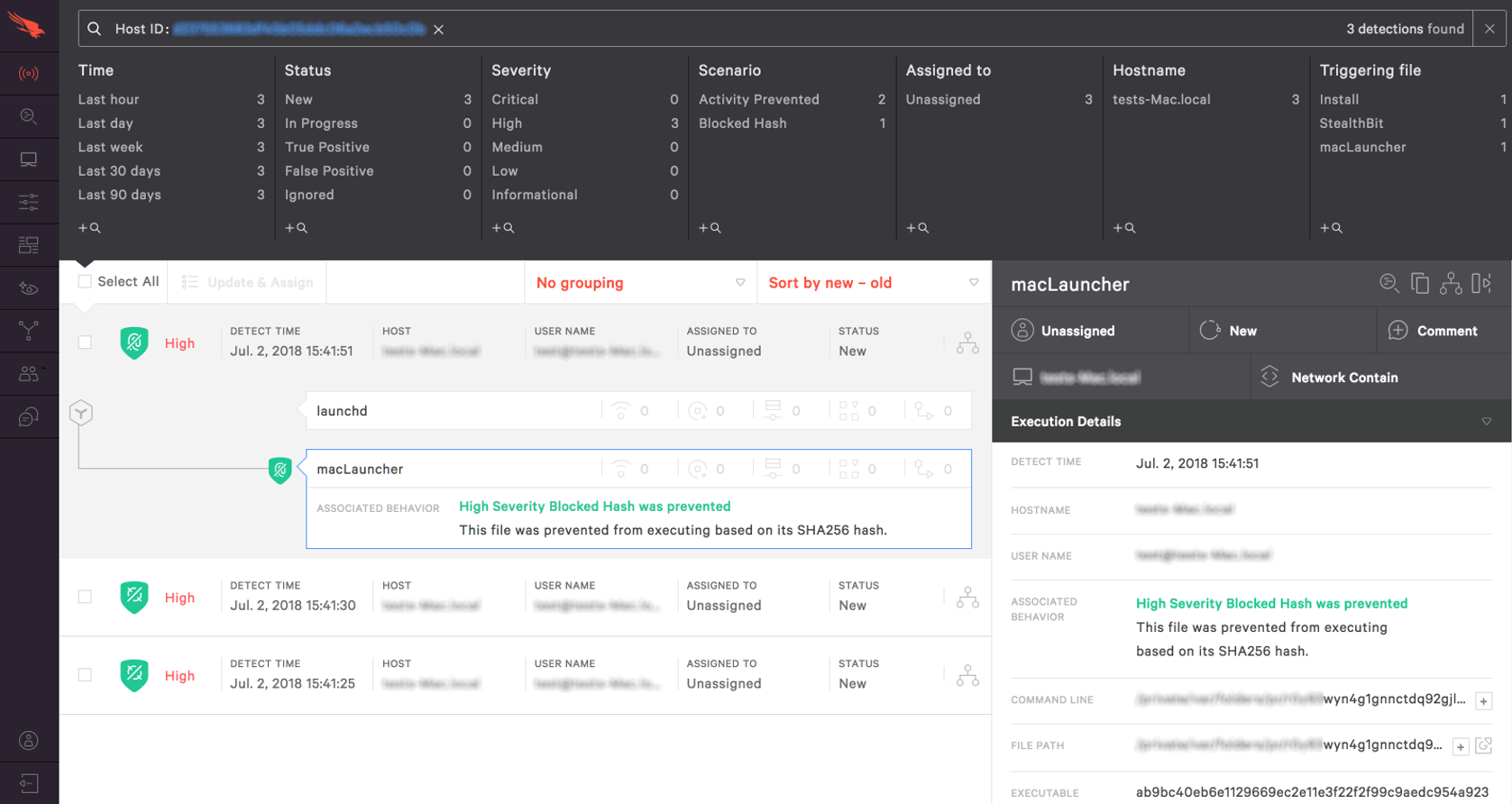
Imagine the dynamics of that for a second. Some of the tested products function also as an incident response, where the system is compromised but a detection alert is reported in the web interface. The move rekindled debate over the merits of independent testing vs vendor-commissioned tests. I used to be 'the Symantec guy on Reddit'. If there was a need to restart the system, it was restarted.
CrowdStrike
Currently these are available mainly for business networks rather than home users. Until we develop a machine learning math model for scripts, our approach is to reduce the attack surface area as any security practitioner would do. They should also endeavor to do their own testing where practical. If we are so controlled by vendors who pay for testing and who allegedly control our testing requirement writing, how can this be? Not all of the products covered here may be available as a trial version. I will read through that. Nobody is performing any of the actual independent models that I am aware of.
What makes for truly independent security product testing?

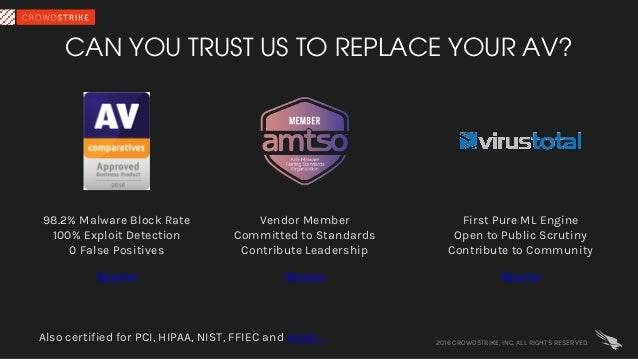
Despite these objections and a vote, the standard has been adopted. Similarly, I saw the post on Crowdstrike's website about VirusTotal, but I have strangely not actually seen Crowdstrike pop up in the results of any files that I have submitted. However, the Magic Quadrant for Endpoint Protection Platforms report from 2016 does not have you guys listed at all: To be honest, I don't put a lot of stock in to Gartner's reports and their Magic Quadrants, but it is another tool for the product evaluation toolbox. We started CrowdStrike five years ago with the mission to revolutionize endpoint security. The argument being, there is no such thing as 100-percent in security.
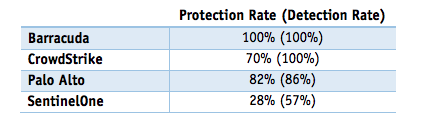
Comparison of “Next

The Cylance rep also missed a meeting with us and was hard to get in touch with sometimes. The first test case the holiday test will focus on products seven days out of date, with no access to the internet — denying them the ability to check cloud-based sources or apply updates. Any use of the results, etc. This can be achieved via blocking the exploit in step 1, 2 or 3. The scores in brackets shows the total detection rate if notifications in the web interface are counted as detections i. Towards the end of 2016, Cylance, a feisty endpoint protection startup out of Irvine, California, published a series of blogs challenging the methods used by two certification labs to conduct endpoint protection tests. We believe their lawsuit is baseless.
Next Gen Antivirus (NGAV): Falcon Prevent
Reachout to me if you want me to explain in more detail. Just a few weeks ago, we we are one of only 2 next-gen endpoint vendors who have put their Machine Learning engines up for public scrutiny in this way and have had — with more due in the coming weeks from other testing houses. But — I must add, there are other variables and features that can make some tools preferred over others. Just unmatched prevention from the get-go. It said, among other things: Testing products in a fair and balanced way is very difficult.