Antivirus signatures palo alto. Solved: Live Community 2019-04-04
Palo Alto Networks aspires to anti
It is cost-effective compared to similar solutions. WildFire technology is being used already by Palo Alto customers, among them Concord Hospital. That is what we call a signature collision. To perform a DoS attack, an attacker might flood a targeted system with traffic or send information that causes it to fail. So these vendors have large teams of people who are constantly churning out signatures based on new threats they observe in the wild. Then the other approach that concerned us was tools focused on post-attack detection or remediation.
Network
Endpoint Protection is the next generation. Hello, please see answers in line. Also, if malware whose signature we disabled should become active again, it is possible and probable we would re-enable the signature regardless of the collision. Symantec has cloud-based endpoint protection, so whether a user is off the network or on the network, the endpoint will be protected by the cloud. Stateful high-availability ensures that your network is always protected.
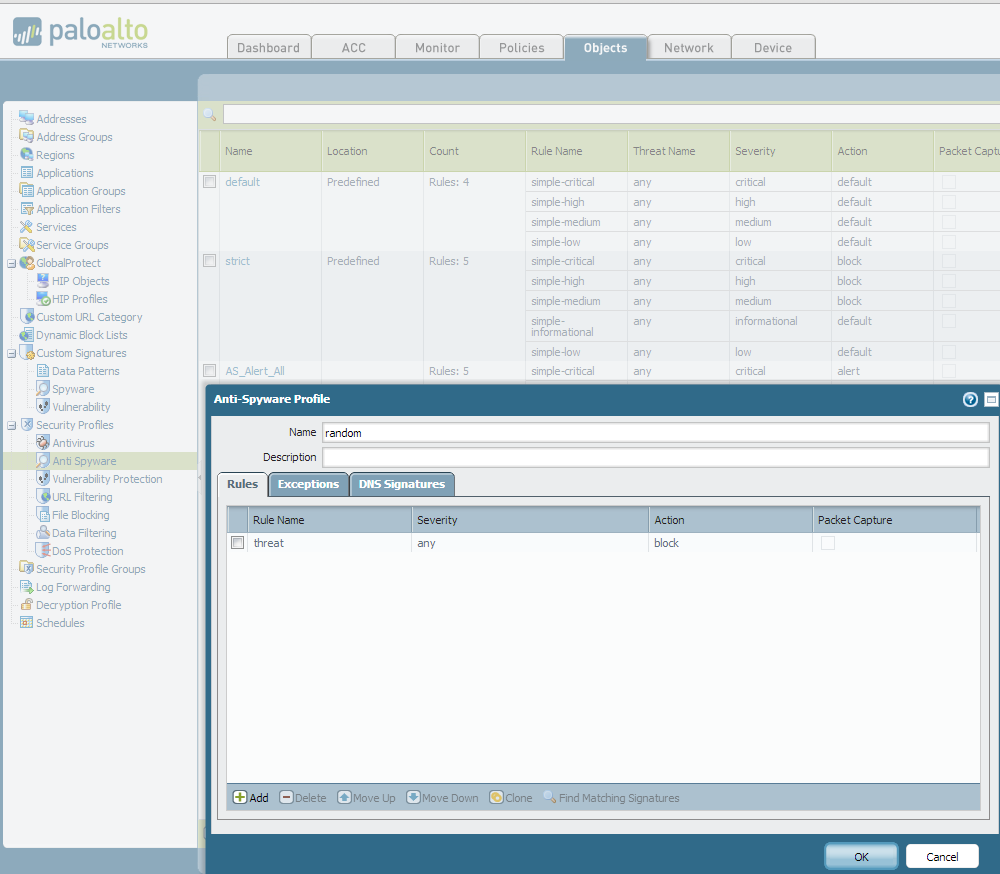
Antivirus Profiles
Enabling applications while blocking unapproved or dangerous files by type Our next-generation firewalls give you the ability to control the flow of a wide range of file types by looking deep within the payload to identify the file type as opposed to looking only at the file extension , to determine if a file transfer is allowed by your policy. In my evaluation, it used a negligible amount of memory and disk space, rendering it virtually invisible in terms of its overall footprint. So when we were looking at making an investment we spent a lot of time in our due diligence looking at the approaches that others use. There are a few negative points. It just came with the renewal, which was nice. The scalability is good, the cross platform legacy capability is great for the companies who do not need to be leading the market with the latest hardware in order to benefit.
Palo Alto says its new endpoint protection tool can stop the bad stuff in its tracks

In terms of a comprehensive security posture, preventing threats should always trump detecting them. The world of malware and exploits has a long history, and anyone involved in this industry knows that we are at a tipping point. Any external device which is inserted into a computer should be subject to an auto-scan policy, to automatically scan it before accepting the device. Control the Data Control access to data and control the movement of data between applications. They should separate the feature for each separate solution for mobile devices.
Why Endpoints Shouldn't Rely Entirely On Scanning
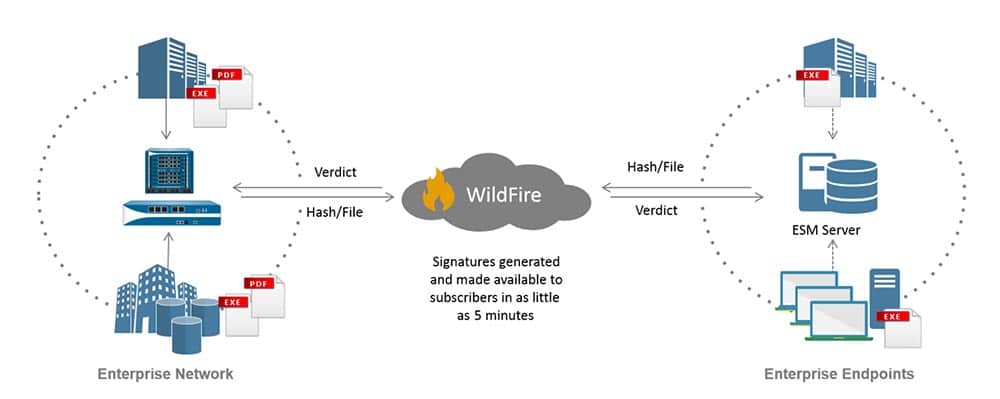
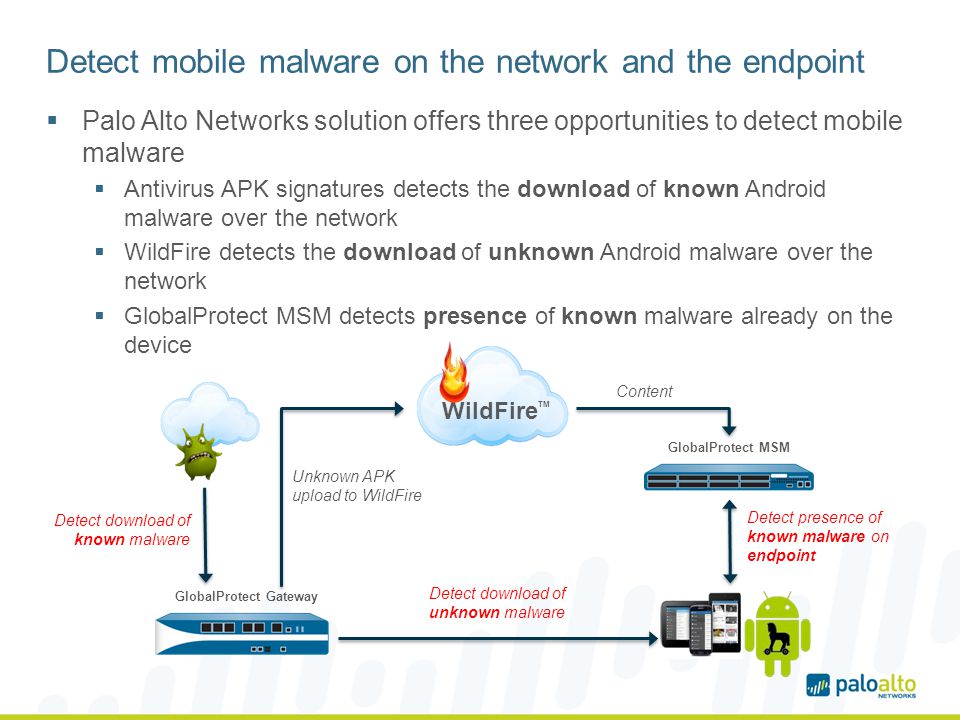
Drop Drops the application traffic. There are obvious reasons for selecting particular bytes for signatures, such as making sure that no bytes common to all files are included in the signature - in that case, all files would always trigger our signatures. New signatures for new malware variants are then generated using our uniform signature format and delivered to customers through scheduled daily or emergency updates. By executing suspect files in a virtual environment and observing their behavior, Palo Alto Networks identifies malware quickly and accurately, even if the malware sample has never been seen before. Adware can also retrieve updates from a command-and-control C2 server and install those updates in a browser or onto a client system. You can easily create log filters by clicking on a cell value, which can then be expanded with additional criteria using the expression builder.
Study: Signature

We didn't have to pay any additional fee for the cloud instance. For each signature type, category, and even specific signatures you can continue to modify or create new profiles to more granularly enforce potential threats. And where can I verify that they have been being updated? Some adware modifies browsers to highlight and hyperlink the most frequently searched keywords on web pages-these links redirect users to advertising websites. Comparative view into traffic and threat patterns App-Scope is a dynamic, customizable window into your network's activity, presenting you with comparative statistics based upon different timeframes, applications, application categories, threat profiles and more. The antivirus engine detects and blocks viruses, spyware phone home, spyware download, known Bots, as well as worms and Trojans. This increasingly popular malware delivery mechanism is known as 'drive-by downloads. When they started they found it very easy; not easy to implement but easy to use.
Traps: Protecting Resource Sensitive Environments
Most of the discovered was being updated every three to six days in order to avoid signature-based antivirus, Palo Alto said. There is no silver bullet in this battle but network security will absolutely continue to play a big role in preventing attacks. Network-based Malware Protection The broadening use of social media, messaging and other, non-work related applications introduces a variety of vectors that can be used to propagate viruses, spyware, worms and other types of malware. The study determined 7% of unknown files encountered in the wild are actually malware and of those malicious files, 57% had no coverage by antivirus signatures. Like scanning, these updates can reduce system performance. Protecting the device also plays an important role for protecting the data as well, because data is not safe on a compromised device.
Palo Alto says its new endpoint protection tool can stop the bad stuff in its tracks

By default, there are some policies which stop us from running properly. Traps, integrated with WildFire, can identify and prevent even the most evasive threats. Antivirus collision is a case where a signature created for one malware file, or one malware family, triggers on the other benign files, unrelated to original files for which the signature was created. You can deploy DoS protection policies based on a combination of elements including type of attack, or by volume both aggregate and classified , with response options including allow, alert, activate, maximum threshold and drop. Antivirus: Network-based Malware Protection The broadening use of social media, messaging and other non-work related applications introduce a variety of vectors for viruses, spyware, worms and other types of malware.
Palo Alto Networks
They don't like to respond to messages when you send them to them. Furthermore, even a purpose-built virtual security product often leaves gaps in the overall security architecture if it is not part of a cohesive security infrastructure. The Palo Alto Networks threat team analyzes the samples and quickly eliminates duplicates and redundancies. This is an engineering decision; we are weighting benefit to the end users - if the malware was not seen recently, and the benign file is required for business continuity, we would disable the signature in favor of the benign file. Protect the network from threats propagated by drive-by downloads. These factors are correlated to create a report that provides you with a list of users that are likely infected, and the behaviors that led to the diagnosis.